Splashtop On-Prem, as the name indicates, is an on-premise solution that is deployed and used in-house. Being installed and configured inside a LAN network, all the endpoint devices, including phones, tablets, laptops and desktops can conveniently connected to the Splashtop Gateway and establish remote sessions between each other.
However, it is common that the users have to access the Splashtop Gateway from an external network, or from the Internet. To make it possible, the Splashtop Gateway has to be deployed properly, with a unique public IP address so that it can be found by others inside the vast cyber world.
There are a few methods to deploy the Splashtop Gateway and make it accessible from the Internet.
- Assign a public IP directly to the Gateway server
- Use port forwarding by router
- Use DMZ network to connect Internet and LAN separately
We'll explain each of the methods in some more details below.
Method 1: Assign a public IP directly to the Gateway server
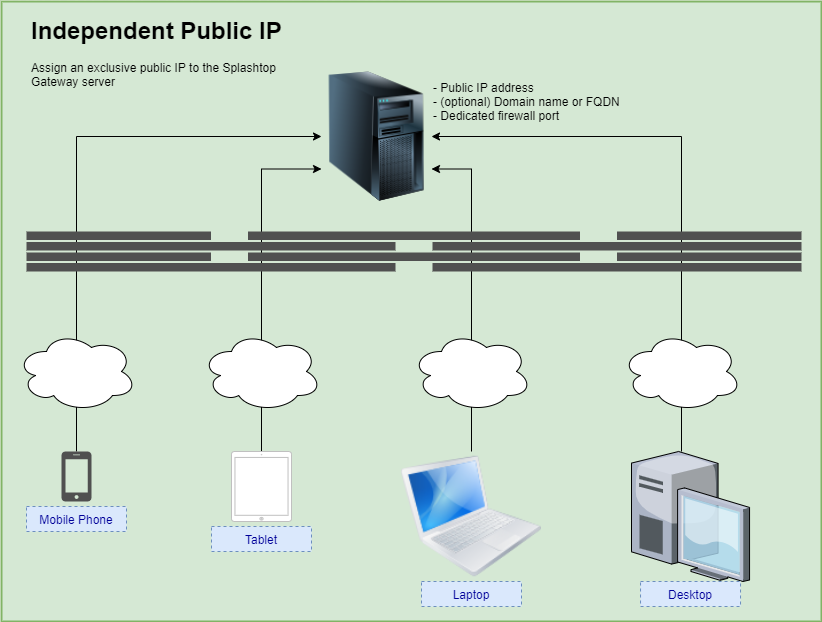
The simplest way to deploy the Splashtop Gateway is to assign a public IP address to the server, which can be hosted in-house (e.g. in a server room) or on the cloud (e.g. Amazon AWS, Oracle OCI, Microsoft Azure).
Because the public IP is exclusively used by the Gateway server, it is now accessible by any device on the Internet using the combination of IP address and designated port number.
Method 2: Use port forwarding by router
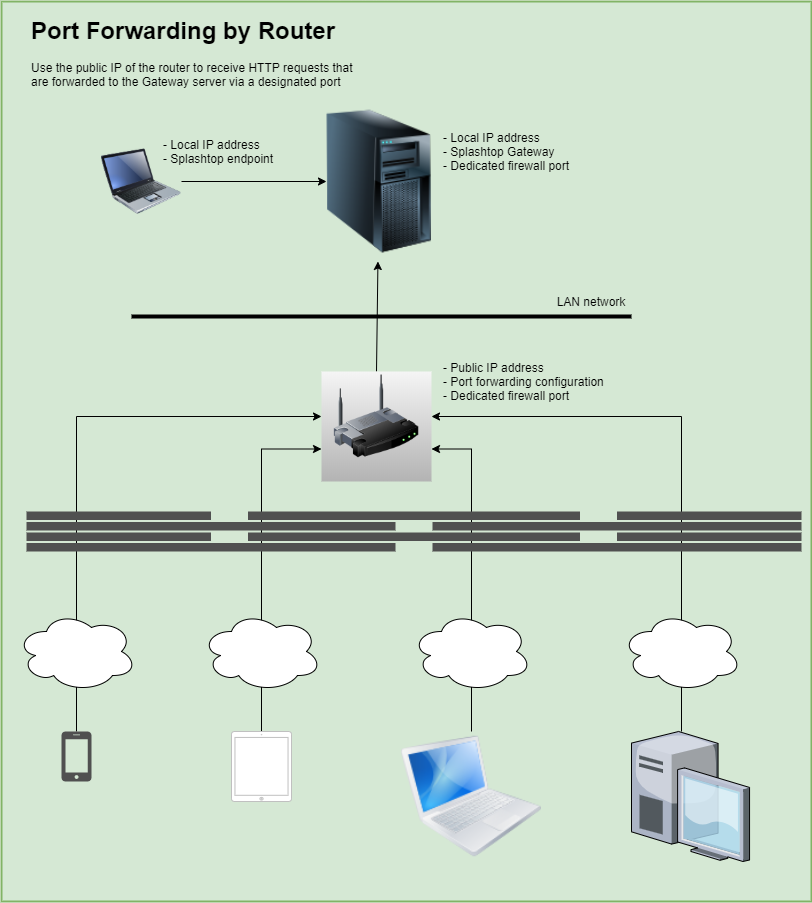
If you have a public IP and it is being used by the router, then port forwarding is your option. Most routers support port forwarding configuration, i.e. redirecting incoming communication from a specific port to another local IP address.
Below is an example of how to set up port forwarding on a router.
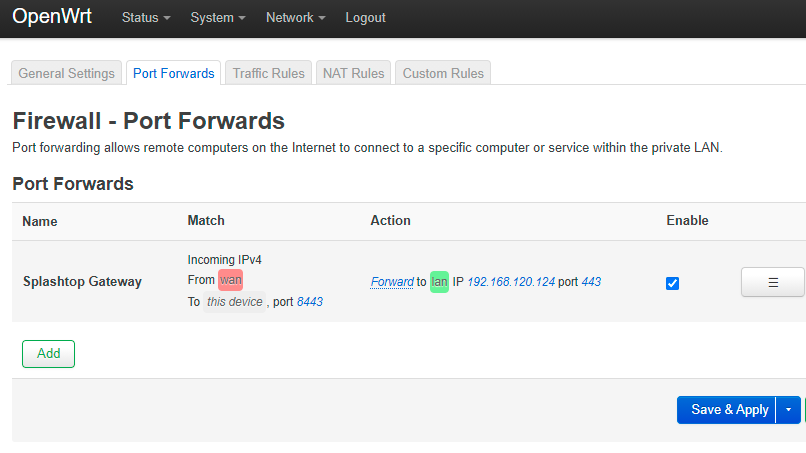
Based on the current configuration, any HTTP/HTTPS requests to the IP address of the router at port 8443 will be forwarded to the local IP 192.168.120.124 at port 443. (assuming HTTPS://192.168.120.124:443 is the Splashtop Gateway portal)
Method 3: Use DMZ network to connect Internet and LAN separately
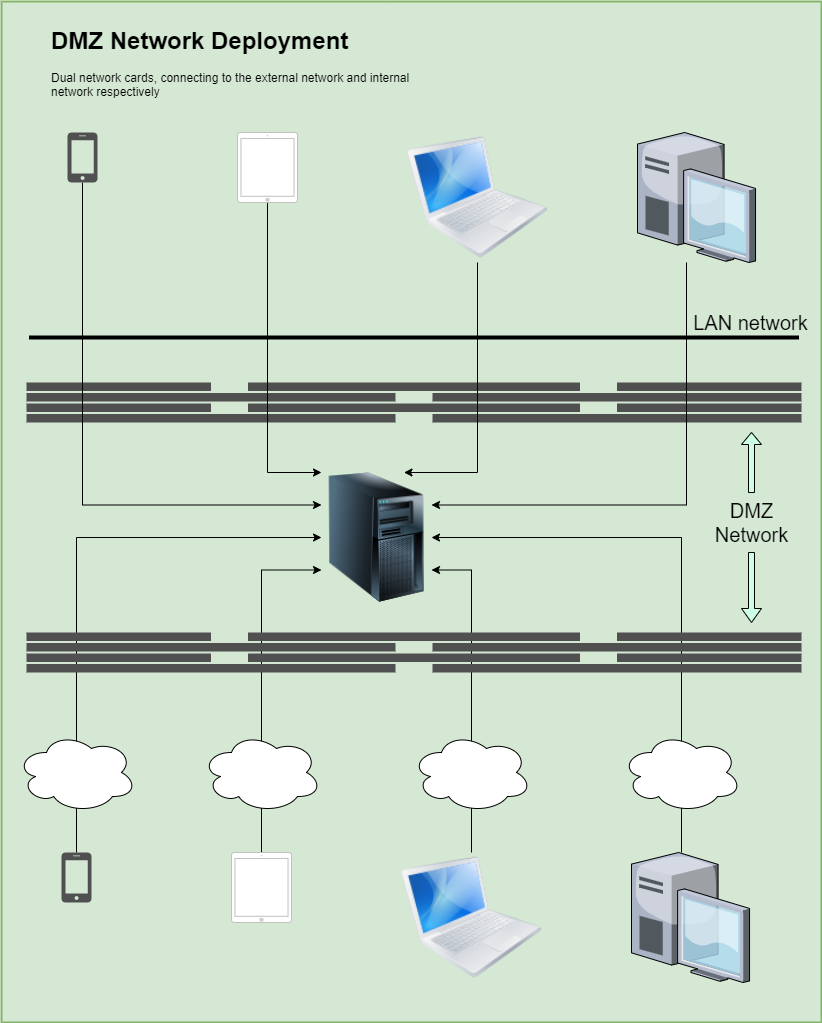
DMZ, or demilitarized zone, is a layer of network sitting between the enterprise LAN network and the Internet, segregated by firewalls between each of the networks. It acts as the buffer zone so that the enterprise LAN network can be protected by avoid exposing directly to the external Internet.
The Splashtop Gateway located in the DMZ network, equipped with dual network cards, however can be accessed by both external Internet and the Enterprise LAN, given the firewalls at both sides are configured properly.
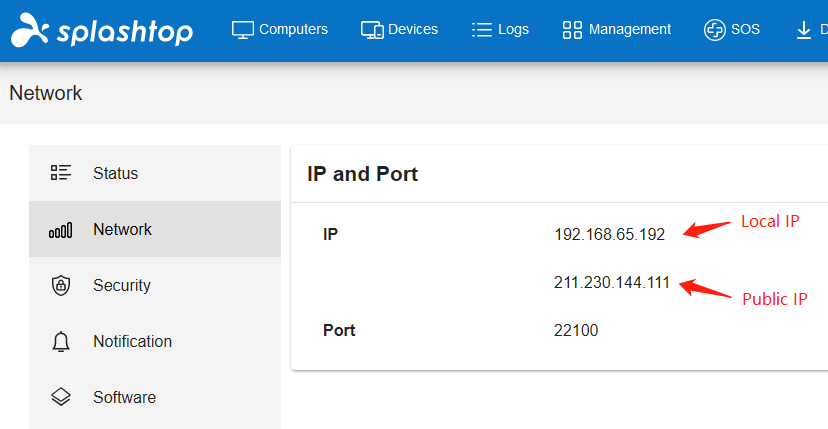
Below is an example of Splashtop Gateway hosted with dual network cards.
The address "https://192.168.65.192:22100" can be used by the devices located in the enterprise LAN network to access the Splashtop Gateway, while "https://211.230.144.111:22100" can be used by the devices located in external Internet to access the same Splashtop Gateway.
Summary
A public IP address is always required in order to make the Splashtop Gateway accessible by the endpoints from the Internet, no matter it is hosted on the cloud, in the office LAN or in the DMZ network.
It may not be always appreciated to use the IP address as the Splashtop Gateway access point. In that case, the IP address can be conveniently mapped to a domain name or FQDN (fully qualified domain name), and the users can then use the IP address or domain name/FQDN interchangeably to access the Splashtop Gateway.